The U.S. has charged a Chinese national for hacking thousands of Sophos firewall devices worldwide in 2020.
The U.S. has charged the Chinese national Guan Tianfeng (aka gbigmao and gxiaomao) for hacking thousands of Sophos firewall devices worldwide in 2020.
Tianfeng worked at Sichuan Silence Information Technology Co., faces charges for developing and testing a zero-day exploit used to compromise approximately 81,000 firewalls.
The man and co-conspirators exploited a zero-day vulnerability, tracked as CVE-2020-12271, in Sophos firewalls to deploy malware. The malware stole data and encrypted files to block remediation attempts.
“Guan and his co-conspirators worked at the offices of Sichuan Silence Information Technology Co. Ltd. to discover and exploit a previously-unknown vulnerability (an “0-day” vulnerability) in certain firewalls sold by U.K.-based Sophos Ltd. (Sophos) – an information technology company that develops and markets cybersecurity products.” reads the press release published by DoJ. “The malware that exploited the vulnerability discovered by Guan was designed to steal information from infected computers and to encrypt files on them if a victim attempted to remediate the infection. In total, Guan and his co-conspirators infected approximately 81,000 firewall devices worldwide, including a firewall device used by an agency of the United States.”
At the end of April 2020, cybersecurity firm Sophos released an emergency patch to address an SQL injection zero-day vulnerability affecting its XG Firewall product that has been exploited in the wild.
Sophos was informed of the attacks exploiting the zero-day issue by one of its customers on April 22, 2020. The customer noticed “a suspicious field value visible in the management interface.”
Sophos investigated the incident and determined that hackers targeted systems configured with either the administration (HTTPS service) or the User Portal exposed on the WAN zone.
The attackers exploited an SQL injection zero-day vulnerability to gain access to exposed XG devices.
“The attack used a previously unknown SQL injection vulnerability to gain access to exposed XG devices.” reads the advisory published by Sophos.
“It was designed to download payloads intended to exfiltrate XG Firewall-resident data. The data for any specific firewall depends upon the specific configuration and may include usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access.” “Passwords associated with external authentication systems such as AD or LDAP are unaffected. At this time, there is no indication that the attack accessed anything on the local networks behind any impacted XG Firewall.”
The hackers exploited the SQL injection flaw to download malicious code on the device that was designed to steal files from the XG Firewall.
Hackers exploited the issue to install the Asnarök Trojan that allowed the attackers to steal files from the XG Firewall and use the stolen info to compromise the network remotely.
The Trojan could steal sensitive data including usernames and hashed passwords for the firewall device admin, and user accounts used for remote access. Login credentials associated with external authentication systems (i.e. AD, LDAP) are not impacted by the flaw.
According to a report published by Sophos at the end of April, the malware employed in the attack can retrieve firewall resident information, including:
- The firewall’s license and serial number
- A list of the email addresses of user accounts that were stored on the device, followed by the primary email belonging to the firewall’s administrator account
- Firewall users’ names, usernames, the encrypted form of the passwords, and the salted SHA256 hash of the administrator account’s password. Passwords were not stored in plain text.
- A list of the user IDs permitted to use the firewall for SSL VPN and accounts that were permitted to use a “clientless” VPN connection.
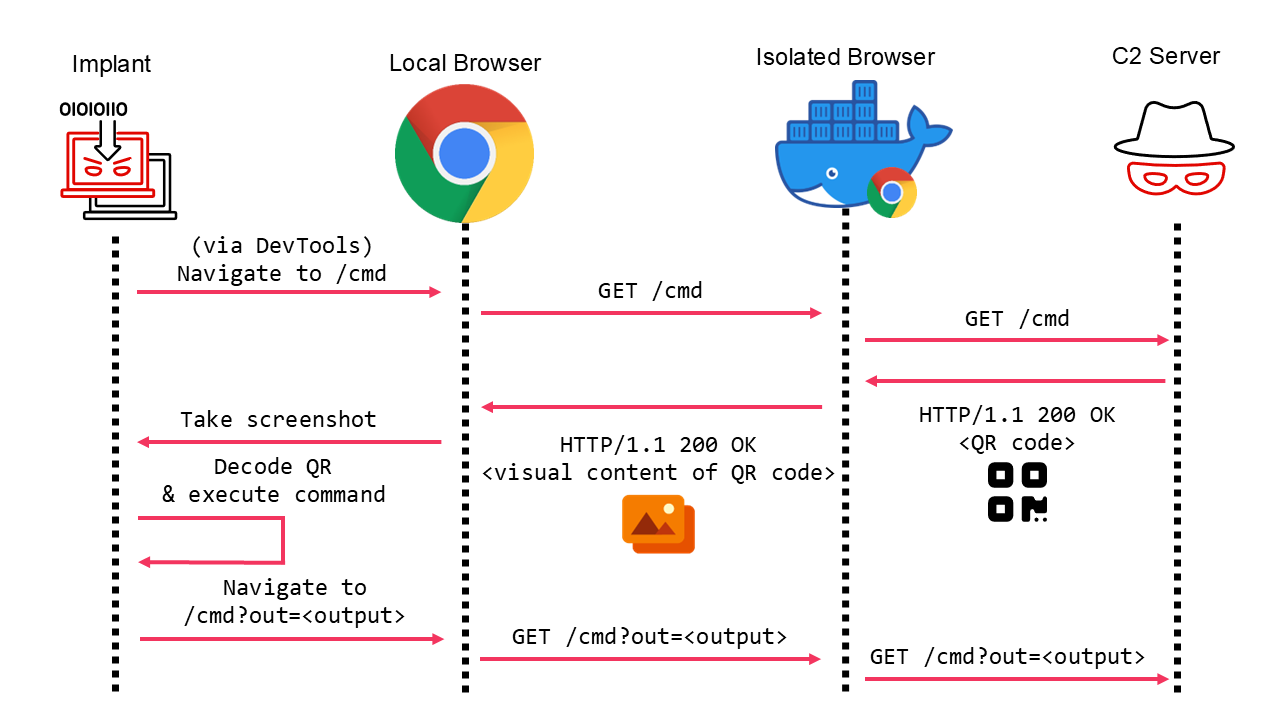
Below is the attack scenario described by Sophos:

Sophos pushed a hotfix to the firewalls after the discovery of the attacks.
This hotfix eliminated the SQL injection vulnerability, stopped the XG Firewall from accessing any infrastructure under the control of the attacks, and cleaned up any remnants from the attack.
Sophos’s update also added a special box in the XG Firewall control panel to allow users to determine if their device has been compromised.
Weeks later, the experts observed a new wave of attacks where hackers exploited the issue to distribute the Ragnarok Ransomware.
“Since we published our first report, the attackers first modified their attack to attempt to use what we previously described as the “backup channel.” This was a Linux shell script that served as a dead man switch—a portion of the attack intended to trigger only under certain circumstances; in this case, if a specific file the attackers created during the attack gets deleted.” continues the report.

To deploy the Ragnarok ransomware, attackers attempted to leverage the EternalBlue and DoublePulsar exploits.
“Ragnarok is a less common threat than other ransomware, and it appears that this threat actor’s modus operandi – and the tooling they employ to deliver this ransomware—is quite different from those of many other threat actors. It was a rare and notable event to observe a Linux ELF application being used to try to spread malware across platforms to Windows computers.” concludes the report.
“This incident highlights the necessity of keeping machines inside the firewall perimeter up to date, and serves as a reminder that any IOT device could be abused as a foothold to reach Windows machines.”
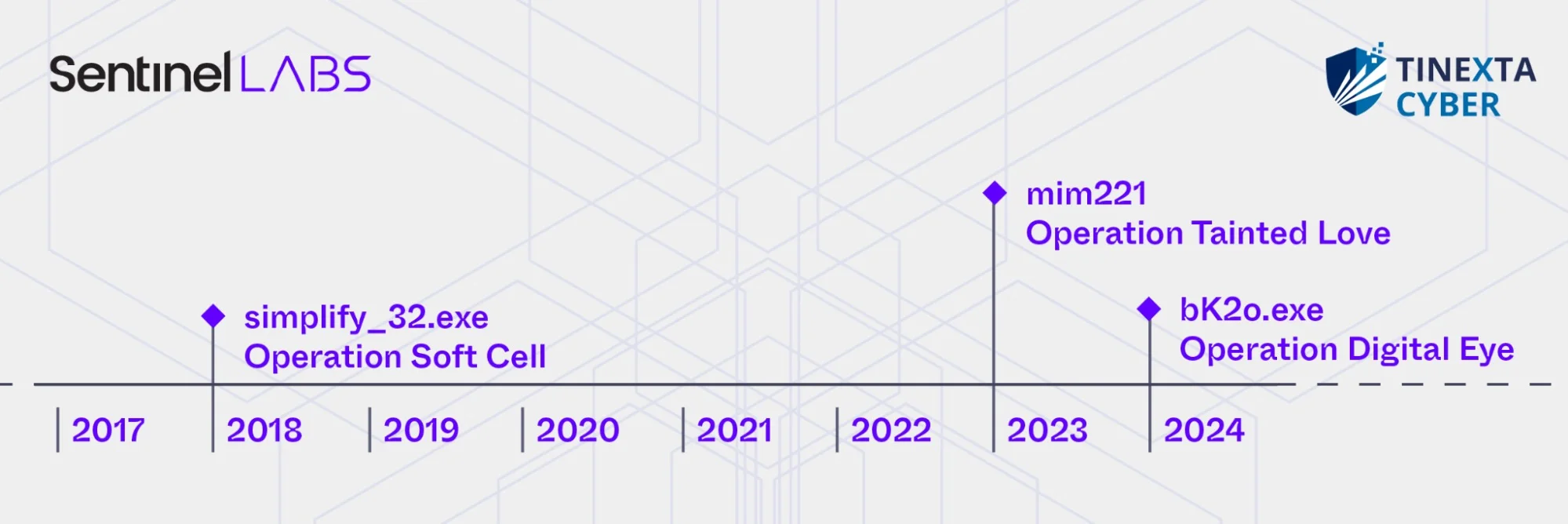
Sophos revealed a years-long “cat-and-mouse” battle with China-linked threat actors, using custom implants to track the attackers’ activities. Since 2018, Sophos has faced increasingly aggressive campaigns, including the India-based Sophos subsidiary Cyberoam, where attackers exploited a wall-mounted display for initial access.

Sophos published a series of reports named ‘Pacific Rim‘ that includes details about the operations conducted by Chinese hackers against network devices of different vendors worldwide for over 5 years.
Sophos, with the help of other cybersecurity firms, government, and law enforcement agencies investigated the cyber attacks and attributed them multiple China-linked APT groups, such as Volt Typhoon, APT31 and APT41/Winnti.
The cyber spies targeted multiple vendors, including Barracuda, Check Point, Cisco, D-Link, Fortinet, Juniper, NetGear, SonicWall, and Sophos.
The threat actors exploited vulnerabilities in networking devices used by businesses to gain a foothold by installing custom malware. Researchers observed the attackers monitoring network communications and stealing credentials from the victims.
The Chinese hackers have also ramped up the use of zero-day vulnerabilities in targeted devices. Sophos researchers suspect that many of these zero-days were identified by Chinese researchers who share them with vendors as well as the Chinese government.
“Sophos X-Ops has identified, with high confidence, exploit research and development activity being conducted in the Sichuan region.” reads the report published by Sophos. “Consistent with China’s vulnerability disclosure legislation, X-Ops assesses with high confidence that the developed exploits were then shared with multiple distinct state-sponsored frontline groups with differing objectives, capabilities, and post-exploitation tooling.”
Sophos observed three evolving tactics in China-linked threat actors:
- A shift from noisy attacks to targeted operations on critical Indo-Pacific infrastructure, including nuclear, military, and government sectors.
- Enhanced stealth techniques, such as using living-off-the-land tactics, memory-only Trojans, a multi-vendor rootkit, and an experimental UEFI bootkit.
- Improved operational security, including disrupting firewall telemetry to hinder detection and minimize their digital footprint.
The first documented attack against a Sophos facility is the one that targeted Cyberoam in 2018. Attackers deployed a remote access trojan (RAT) on a display computer, initially suggesting an unsophisticated actor. However, further investigation revealed a complex rootkit, “Cloud Snooper,” and a unique cloud pivoting technique via a misconfigured AWS SSM Agent. Sophos researchers speculate the attack was part of an intelligence-gathering campaign aimed at developing malware for network devices.
Between 2020 and 2022, attackers launched multiple campaigns to exploit zero-day vulnerabilities in publicly accessible network appliances, focusing on WAN-facing services. Successful exploitation of these vulnerabilities could allow attackers to steal sensitive data, inject firmware payloads, and even reach LAN-connected devices. Sophos identified and publicly disclosed these attacks, including campaigns like Asnarök and “Personal Panda,” while warning vulnerable organizations of the risks. Sophos also found possible links between Chinese researchers, including a research community in Chengdu, and state-sponsored actors, suggesting shared vulnerability research with vendors and Chinese government entities.
Since mid-2022, threat actors shifted to targeted, manual attacks on high-value targets like government agencies, critical infrastructure, R&D, healthcare, and finance. The attackers used stealthy techniques, they employed a custom userland rootkits, the TERMITE in-memory dropper, Trojanized Java files, and an experimental UEFI bootkit on test devices. Attackers maintained persistence through VPN credentials, Active Directory DCSYNC access, and firmware-hooking methods to survive updates. While known CVEs were commonly used for initial access, attackers also utilized valid admin credentials on LAN-facing devices for prolonged access.
The attackers behind these campaigns became increasingly sophisticated in their tactics. They actively worked to evade detection by Sophos.
“Guan and his co-conspirators designed the malware to steal information from firewalls. To better hide their activity, Guan and his co-conspirators registered and used domains designed to look like they were controlled by Sophos, such as sophosfirewallupdate.com. Sophos discovered the intrusion and remediated its customers’ firewalls in approximately two days, which caused the co-conspirators to modify their malware.” reads the advisory. “As modified, the malware was designed to deploy encryption software from a ransomware variant in the event the victims attempted to remove the malware. Their encryption efforts did not succeed, but demonstrated the conspirators’ disregard for the harm that they would cause to victims.”
The U.S. Treasury’s OFAC has sanctioned Sichuan Silence Information Technology Co. Ltd. and its employee Guan Tianfeng for hacking U.S. critical infrastructure companies. Sichuan Silence, a Chengdu-based contractor for Chinese intelligence agencies, provides tools for network exploitation, email monitoring, brute-force attacks, and public sentiment suppression. It also supplies equipment for targeting and exploiting network routers.
The U.S. Department of State is offering rewards of up to $10 million for information on Sichuan Silence, Guan Tianfeng, or others involved in cyberattacks targeting U.S. critical infrastructure on behalf of foreign governments.
“Today, the Department of the Treasury’s Office of Foreign Assets Control (OFAC) is sanctioning cybersecurity company Sichuan Silence Information Technology Company, Limited (Sichuan Silence), and one of its employees, Guan Tianfeng (Guan), both based in People’s Republic of China (PRC), for their roles in the April 2020 compromise of tens of thousands of firewalls worldwide. Many of the victims were U.S. critical infrastructure companies.” reads the press release published by U.S. Treasury’s OFAC