A vulnerability in Nuclei, an open-source vulnerability scanner, could allow attackers to bypass signature checks and execute malicious code.
A high-severity security flaw, tracked as CVE-2024-43405 (CVSS score of 7.4), in the open-source vulnerability scanner ProjectDiscovery’s Nuclei, could allow attackers to bypass signature checks and execute malicious code.
The Wiz’s engineering team discovered the vulnerability.
The vulnerability arises from newline handling discrepancies and multi-signature processing, enabling attackers to inject malicious content into templates.
“A vulnerability has been identified in Nuclei’s template signature verification system that could allow an attacker to bypass the signature check and possibly execute malicious code via custom code template.” reads the advisory published on GitHub. “The vulnerability stems from a discrepancy between how the signature verification process and the YAML parser handle newline characters, combined with the way multiple signatures are processed. This allows an attacker to inject malicious content into a template while maintaining a valid signature for the benign part of the template.”
The vulnerability impacts all versions of Nuclei later than 3.0.0, it was addressed in version v3.3.2.
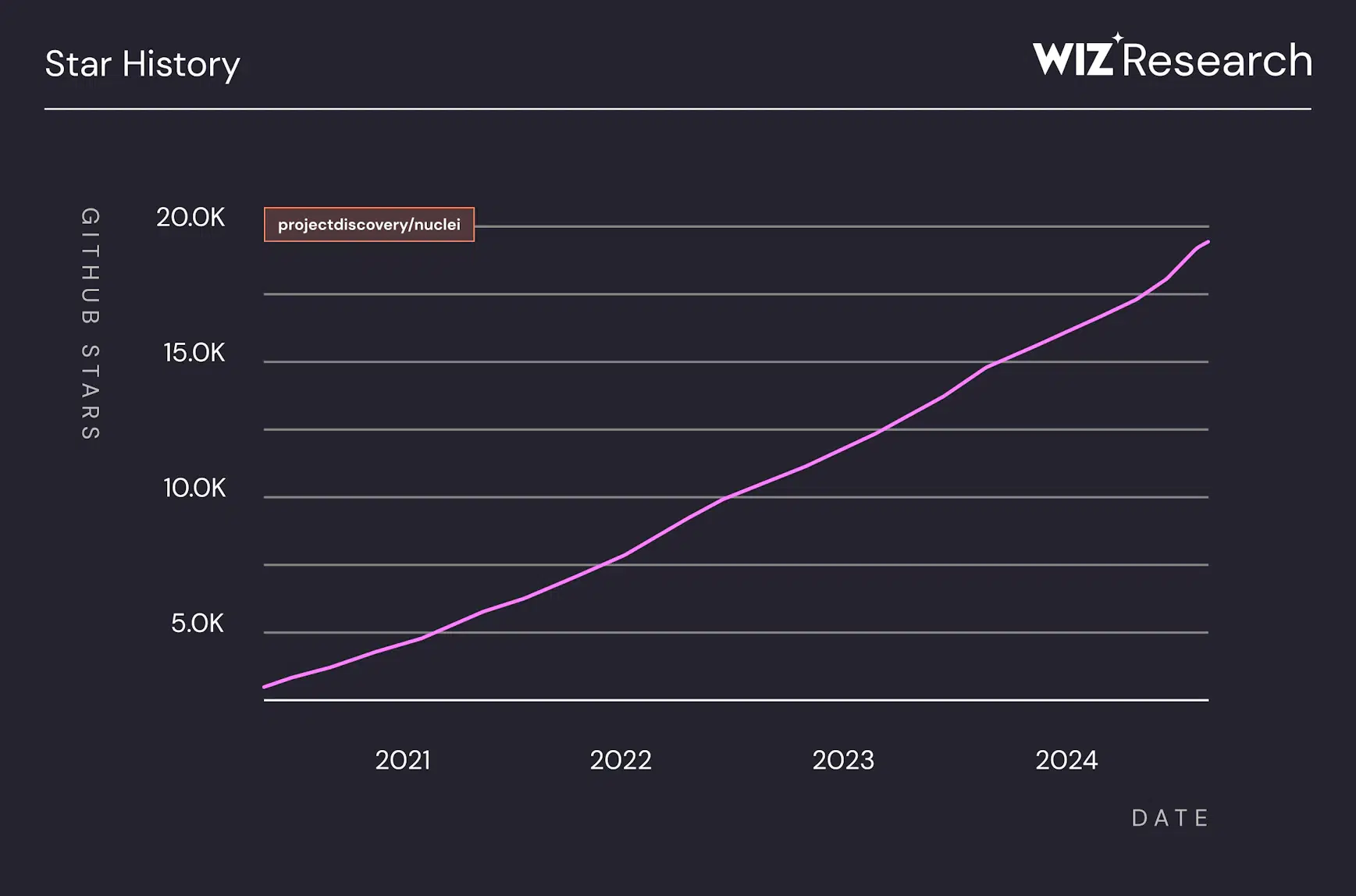
The vulnerability scanner has 21,000+ GitHub stars and 2.1M+ downloads, Wiz researchers pointed out that the software is vital for the security community, highlighting the need to address vulnerabilities.

Nuclei’s strength is its flexible YAML-based templates, enabling detection of vulnerabilities and misconfiguration.
Nuclei supports multiple protocols, including HTTP, TCP, DNS, TLS, and Code. The code protocol allows the execution of external code on the host operating system, experts warn that this feature could pose serious risks.
Nuclei templates using the code protocol can assess system security but risk executing malicious code locally, potentially compromising servers or infrastructure.
“The flexibility of Nuclei templates means they can be crafted for legitimate or malicious purposes. For instance, the following template demonstrates how an attacker might exploit the code protocol to exfiltrate sensitive data from the host running the template” reads the report published by Wiz.
Nuclei uses signature verification to ensure template integrity, but its reliance on this single mechanism creates a critical point of failure, highlighting the need for robust validation.
Wis researchers said the issue arises from using regex for signature validation alongside a YAML parser, allowing attackers to exploit parsing conflicts with “\r” characters to bypass verification. Parsing inconsistencies allow attackers to use “\r” to add a second “# digest:” line, bypassing signature verification while being executed by the YAML parser.
This exploit is possible due to the following key weaknesses:
- Parser Inconsistencies: Go’s regex-based signature verification treats
\\ras part of the same line, while the YAML parser interprets it as a line break. This mismatch allows attackers to inject content that bypasses verification but is executed by the YAML parser. - First-Signature Trust: The verification logic validates only the first
# digest:line. Additional# digest:lines are ignored during verification but remain in the content to be parsed and executed by YAML. - Inconsistent Signature Removal: The
ReplaceAllfunction removes all# digest:lines from the hashed content, ensuring only the first line is verified. Malicious content in subsequent lines remains unverified but executable.
An attacker can chain these weaknesses to inject unverified, executable content into Nuclei templates.
“An attack vector for this vulnerability arises when organizations run untrusted or community-contributed templates without proper validation or isolation. Additionally, services that allow users to modify or upload Nuclei templates, such as automated scanning platforms or shared security pipelines, become particularly vulnerable.” concludes the report. “An attacker could exploit this functionality to inject malicious templates, leading to arbitrary command execution, data exfiltration, or system compromise.”