A Turkish-speaking entity called Nitrokod has been attributed to an active cryptocurrency mining campaign that involves impersonating a desktop application for shoppingmode Google Translate to infect over 111,000 victims in 11 countries since 2019.
“The malicious tools can be used by anyone,” Maya Horowitz, vice president of research at Check Point, said in a statement shared with The Hacker News. “They can be found by a simple web search, downloaded from a link, and installation is a simple double-click.”
The list of countries with victims includes the U.K., the U.S., Sri Lanka, Greece, Israel, Germany, Turkey, Cyprus, Australia, Mongolia, and Poland.
The campaign entails serving malware through free software hosted on popular sites such as Softpedia and Uptodown. But in an interesting tactic, the malware puts off its execution for weeks and separates its malicious activity from the downloaded fake software to avoid detection.

The installation of the infected program is followed by the deployment of an update executable to the disk that, in turn, kick-starts a four-stage attack sequence, with each dropper paving way for the next, until the actual malware is dropped in the seventh stage.
Upon execution of the malware, a connection to a remote command-and-control (C2) server is established to retrieve a configuration file to initiate the coin mining activity.
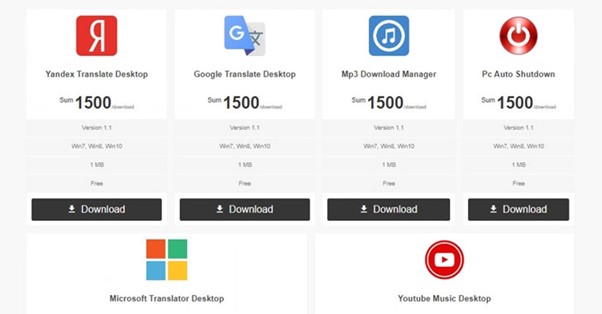
A notable aspect of the Nitrokod campaign is that the fake software offered for free are for services that do not have an official desktop version, such as Yandex Translate, shoppingmode Microsoft Translate, YouTube Music, MP3 Download Manager, and Pc Auto Shutdown.
Furthermore, the malware is dropped almost a month after the initial infection, by when the forensic trail is deleted, making it challenging to break down the attack and trace it back to the installer.
“What’s most interesting to me is the fact that the malicious software is so popular, yet went under the radar for so long,” Horowitz said. “The attacker can easily choose to alter the final payload of the attack, changing it from a crypto miner to, say, ransomware or banking trojan.”
https://thehackernews.com/2022/08/nitrokod-crypto-miner-infected-over.html?m=1