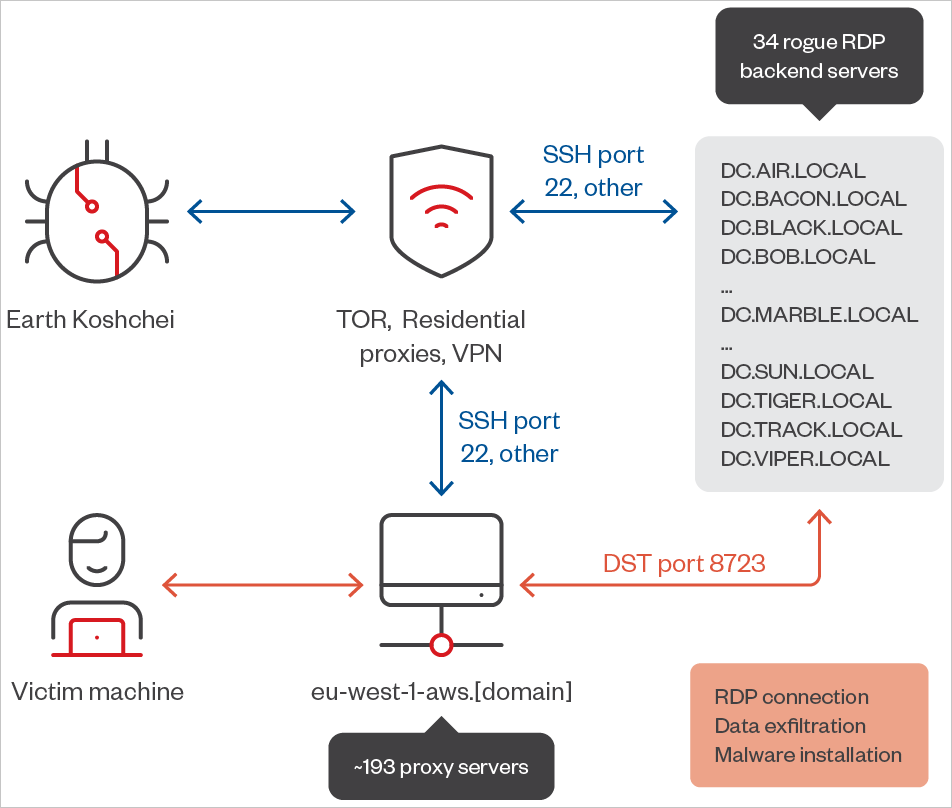
The Russian hacking group tracked as APT29 (aka “Midnight Blizzard”) is using a network of 193 remote desktop protocol proxy servers to perform man-in-the-middle (MiTM) attacks to steal data and credentials and to install malicious payloads.
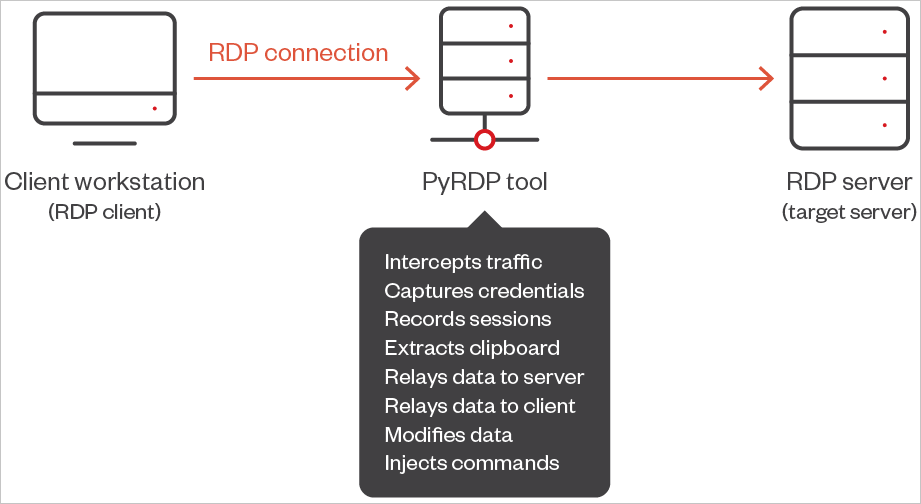
The MiTM attacks utilized the PyRDP red team proxy tool to scan the victims’ filesystems, steal data in the background, and remotely execute rogue applications on the breached environment.
Trend Micro, which tracks the threat actors as ‘Earth Koshchei,’ reports that this campaign targets government and military organizations, diplomatic entities, IT and cloud service providers, and telecommunication and cybersecurity companies.
The domain names registered for the campaign suggest that APT29 targeted entities primarily in the U.S., France, Australia, Ukraine, Portugal, Germany, Israel, France, Greece, Turkey, and the Netherlands.
Using PyRDP for MitM attacks
Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft that allows users to remotely access and control another computer over a network. It is commonly used for remote administration, technical support, and connecting to systems in enterprise environments.
In October 2024, Amazon and CERT-UA published reports confirming that APT29 is tricking victims into connecting to rogue RDP servers after running a file attached to phishing emails.
Once the connection is set up, local resources, including disks, networks, printers, the clipboard, audio devices, and COM ports, are shared with the attacker-controlled RDP server, enabling them unconditional access to sensitive information.
Trend Micro’s latest report reveals more details about this activity after identifying 193 RDP proxy servers that redirected connections to 34 attacker-controlled backend servers, allowing the attackers to monitor and intercept RDP sessions.
The hackers use a Python “man-in-the-middle” MitM red team tool called PyRDP to intercept all communication between the victim and the remote session, allowing the connection to appear legitimate.
The tool allows the attackers to log plaintext credentials or NTLM hashes, steal clipboard data, steal transferred files, steal data from shared drives in the background, and run console or PowerShell commands on new connections.
The researchers explain that this technique was first described by Mike Felch in 2022, who may have inspired APT29’s tactics.
“Upon establishing the connection, the rogue server mimics the behavior of a legitimate RDP server and exploits the session to carry out various malicious activities,” explains Trend Micro
“A primary attack vector involves the attacker deploying malicious scripts or altering system settings on the victim’s machine.”
“Additionally, the PyRDP proxy facilitates access to the victim’s file system, enabling the attacker to browse directories, read or modify files, and inject malicious payloads.
Source: Trend Micro
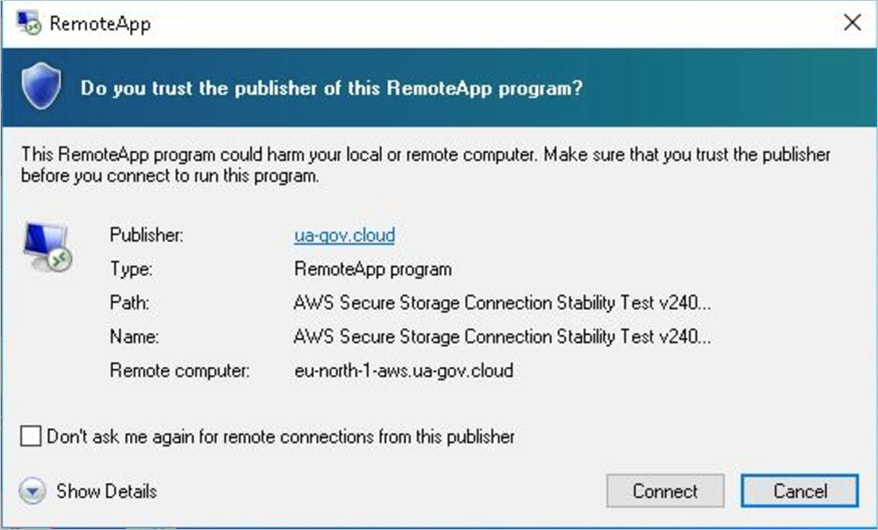
Among the malicious configurations Trend Micro analyzed, there’s also one that serves the user with a misleading AWS Secure Storage Connection Stability Test connection request.
Source: Trend Micro
Regarding APT29’s evasion, the researchers report that the Russian hackers use a combination of commercial VPN products accepting cryptocurrency payments, TOR exit nodes, and residential proxy services to obscure the IP addresses of the rogue RDP servers.
Source: Trend Micro
Defending against rogue RDP configurations requires a good response to malicious emails, which, in this case, were sent from legitimate addresses compromised before the campaign’s launch.
Even more important, Windows users should only make RDP connections to known, trusted servers and never utilize RDP connections sent via email attachments.



