An unconventional data exfiltration method leverages a previously undocumented covert channel to leak sensitive information from air-gapped systems.
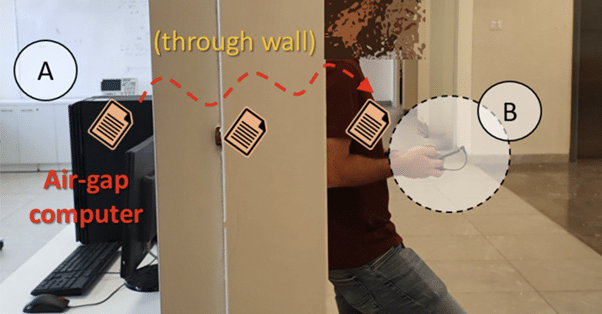
“The information emanates from the air-gapped computer over the air to a distance of 2 m and more and can be picked up by a nearby insider or spy with a mobile phone or laptop,” Dr. Mordechai Guri, the head of R&D in the Cyber Security Research Center in the Ben Gurion University of the Negev in Israel and the head of Offensive-Defensive Cyber Research Lab, said in a new paper shared with The Hacker News.
The mechanism, dubbed COVID-bit, leverages malware planted on the machine to generate electromagnetic radiation in the 0-60 kHz frequency band that’s subsequently transmitted and picked up by a stealthy receiving device in close physical proximity.
This, in turn, is made possible by exploiting the dynamic power consumption of modern computers and manipulating the momentary loads on CPU cores.
COVID-bit is the latest technique devised by Dr. Guri this year, after SATAn, GAIROSCOPE, and ETHERLED, which are designed to jump over air-gaps and harvest confidential data.
Air-gapped networks, despite their high level of isolation, can be compromised by various strategies such as infected USB drives, supply chain attacks, and even rogue insiders.
Exfiltrating the data after breaching the network, however, is a challenge due to the lack of internet connectivity, necessitating that attackers concoct special methods to deliver the information.
The COVID-bit is one such covert channel that’s used by the malware to transmit information by taking advantage of the electromagnetic emissions from a component called switched-mode power supply (SMPS) and using a mechanism called frequency-shift keying (FSK) to encode the binary data.

“By regulating the workload of the CPU, it is possible to govern its power consumption and hence control the momentary switching frequency of the SMPS,” Dr. Guri explains.
“The electromagnetic radiation generated by this intentional process can be received from a distance using appropriate antennas” that cost as low as $1 and can be connected to a phone’s 3.5 mm audio jack to capture the low-frequency signals at a bandwidth of 1,000 bps.
The emanations are then demodulated to extract the data. The attack is also evasive in that the malicious code doesn’t require elevated privileges and can be executed from within a virtual machine.
An evaluation of the data transmissions reveals that keystrokes can be exfiltrated in near real-time, with IP and MAC addresses taking anywhere between less than 0.1 seconds to 16 seconds, depending on the bitrate.
Countermeasures against the proposed covert channel include carrying out dynamic opcode analysis to flag threats, initiate random workloads on the CPU processors when anomalous activity is detected, and monitoring or jamming signals in the 0-60 kHz spectrum.
https://thehackernews.com/2022/12/covid-bit-new-covert-channel-to.html