Zusammenfassung
Dieser Artikel bietet einen praktischen Leitfaden für die Entwicklung einer Erkennungsstrategie für Lightweight Directory Access Protocol (LDAP)-basierte Angriffe. Wir analysieren reale Beispiele für den Missbrauch von LDAP-Attributen durch nationalstaatliche und cyberkriminelle Bedrohungsakteure. Außerdem werden gängige LDAP-Aufzählungsabfragen untersucht und ihre potenziellen Risiken bewertet.
LDAP ist ein leistungsfähiges Protokoll für den Zugriff auf und die Verwaltung von Verzeichnisdiensten wie Active Directory. LDAP wird von Kriminellen häufig für laterale Bewegungen und die Aufzählung kritischer Ressourcen bei Cyberangriffen vor Ort verwendet. Bedrohungsakteure verwenden auch häufig Tools wie BloodHound und SharpHound, die LDAP für böswillige Zwecke ausnutzen.
Die Unterscheidung zwischen gutartiger und bösartiger LDAP-Aktivität innerhalb einer Organisation ist eine Herausforderung. Die große Menge an gutartigen Ereignisprotokollen, die von einem Domänencontroller generiert werden, macht sowohl das Sammeln als auch das Erkennen bösartiger LDAP-Aktivitäten extrem schwierig.
Die Kunden von Palo Alto Networks sind durch Cortex XDR, XSIAM und Xpanse besser gegen LDAP-basierte Angriffe geschützt, auf die wir in der Schlussfolgerung näher eingehen.
Wenn Sie glauben, dass Sie kompromittiert worden sein könnten oder ein dringendes Problem haben, wenden Sie sich bitte an das Referat 42 - Incident Response Team.
| Verwandte Themen des Referats 42 | Cyberkriminalität, Ransomware |
Was ist LDAP?
LDAP ist ein grundlegendes Protokoll, das in fast jeder Windows-Umgebung verwendet wird und Administratoren den Zugriff auf Verzeichnisdienste wie Active Directory ermöglicht. Dieses Protokoll wird für die Verwaltung von Benutzern und Gruppen verwendet und ermöglicht es Anwendungen, Verzeichnisdaten im Hintergrund abzufragen. Obwohl es von Microsoft entwickelt wurde und hauptsächlich in Windows-Umgebungen eingesetzt wird, ist LDAP herstellerunabhängig und kann auch auf Nicht-Windows-Systemen wie macOS und Linux verwendet werden.
Bedrohungsakteure nutzen LDAP häufig, weil seine Funktionen so nützlich sind. APT-Gruppen (Advanced Persistent Threats) und andere Angreifer nutzen LDAP häufig zur Aufzählung von Netzwerken in der Erkundungsphase eines Angriffs. Die Angreifer fragen Verzeichnisse ab, um sensible Informationen wie Benutzerkonten, Gruppenmitgliedschaften und Berechtigungen zu extrahieren, die sie dann dazu verwenden, ihre Privilegien zu erweitern und kritische Ressourcen anzugreifen.
Die Entwicklung von LDAP-Protokollen und -Tools
LDAP hat sich seit seiner Einführung in den frühen 1990er Jahren erheblich weiterentwickelt und an die sich ändernden Anforderungen von Verzeichnisdiensten und Sicherheitsanforderungen angepasst. Nachfolgend finden Sie zwei Beispiele für Änderungen in den neueren Versionen von LDAP:
- LDAP über SSL (LDAPS): Diese sichere Version von LDAP verschlüsselt die Daten während der Übertragung und schützt so sensible Informationen vor dem Abfangen während der Kommunikation.
- Active Directory-Webdienste (ADWS): Dies bietet einen REST-Ansatz für die Interaktion mit Verzeichnisdiensten. ADWS-Tools operieren oft unter dem Radar herkömmlicher Überwachungssysteme, da sie keinen direkten LDAP-Datenverkehr erzeugen.
Tools wie BloodHound und der C#-Datensammler SharpHound haben sich parallel zu diesen Protokollen entwickelt, um Active Directory-Umgebungen zu visualisieren und zu analysieren. SOAPHound baut auf diesen Fortschritten auf, indem es ADWS zur Aufzählung von Active Directory-Daten verwendet.
LDAP-Protokolle: Sichtbarkeit und Herausforderungen
Die große Menge der von LDAP erzeugten Protokolldaten kann Erkennungssysteme überfordern und die Identifizierung bösartiger Aktivitäten erschweren. Es werden so viele Protokolldaten erzeugt, weil es von vielen Systemen und Anwendungen verwendet wird.
Gängige Prozesse wie Outlook erzeugen beispielsweise LDAP-Protokolle, was die umfassende Rolle des Protokolls bei Verzeichnisdiensten verdeutlicht. Diese weit verbreitete Verwendung bedeutet, dass bösartige LDAP-Aktivitäten im Rauschen des normalen Betriebs untergehen können.
Um das LDAP-Protokollvolumen effektiv zu verwalten, sollten Sie sich darauf konzentrieren, relevante Daten zu filtern, wie z. B.:
- Setzen Sie Prioritäten bei der Filterung: Konzentrieren Sie sich auf Protokolle, die auf der Art des Kontos oder des Dienstes basieren, der sie erzeugt, um das Rauschen zu reduzieren.
- Systemgenerierte Abfragen ausschließen: Filtern Sie Abfragen heraus, bei denen es unwahrscheinlich ist, dass sie auf vom Benutzer initiierte Aktionen hinweisen.
Um diese Herausforderungen zu bewältigen, bietet Windows eine native Protokollierung von LDAP-Aktivitäten aus den folgenden Quellen:
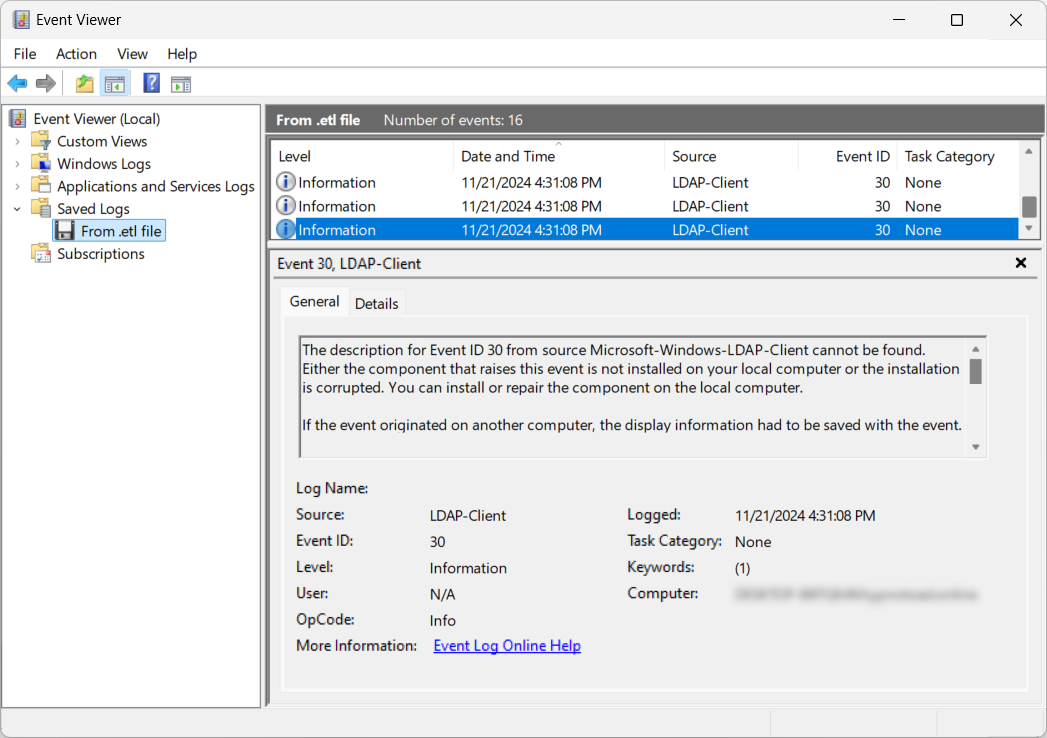
- Microsoft-Windows-LDAP-Client - Ereignis-ID 30: Systemadministratoren können die Debug-Protokollierung für LDAP-Clients aktivieren, um Aktivitäten auf dem initiierenden Host zu verfolgen. Dadurch werden Details wie der auslösende Prozess, der Sucheintrag, der Filter und der Suchbereich protokolliert, wenn auf LDAP über die LDAP-Client-API durch wldap32.dll zugegriffen wird. Abbildung 1 zeigt einen Eintrag mit der Ereignis-ID 30 aus den Debug-Protokollen eines LDAP-Clients.
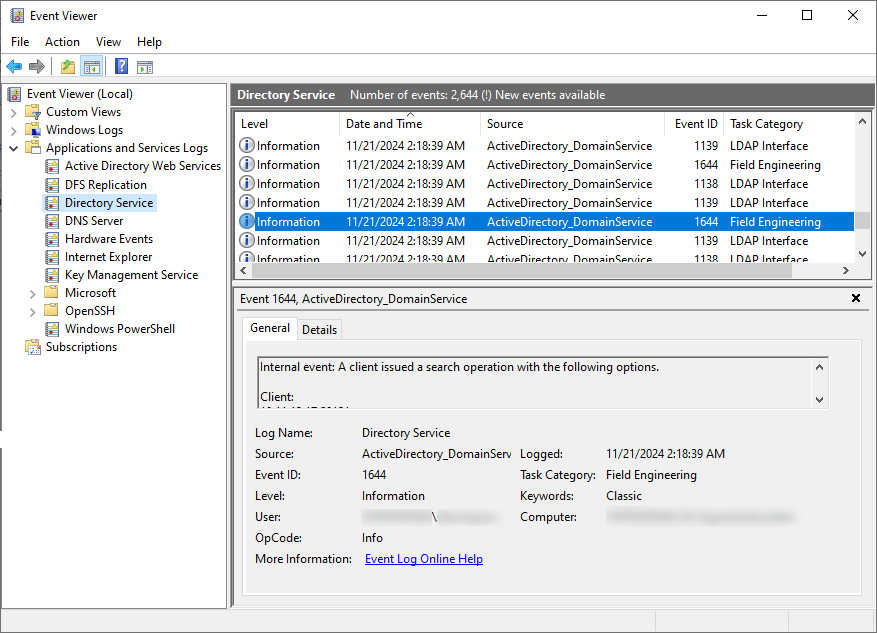
- Microsoft-Windows-ActiveDirectory_DomainService - Ereignis-ID 1644: Damit werden teure, ineffiziente oder langsame LDAP-Abfragen an Domänencontroller von allen interagierenden Hosts erfasst. Beachten Sie, dass diese Ereignis-ID nicht standardmäßig aktiviert ist und zur Aktivierung Aktualisierungen der Windows-Registrierung erfordert. Abbildung 2 zeigt einen Eintrag mit der Ereignis-ID 1644 in der Ereignisanzeige.
Praktische Szenarien für die LDAP-Aufzählung
Dieser Abschnitt enthält Beispiele aus der Praxis, in denen Angreifer LDAP-Enumerationstools in Active Directory-Umgebungen einsetzen.
Stattlicher Stier in Verbindung mit der Nutzung von AdFind bei Angriffen auf die südostasiatische Regierung
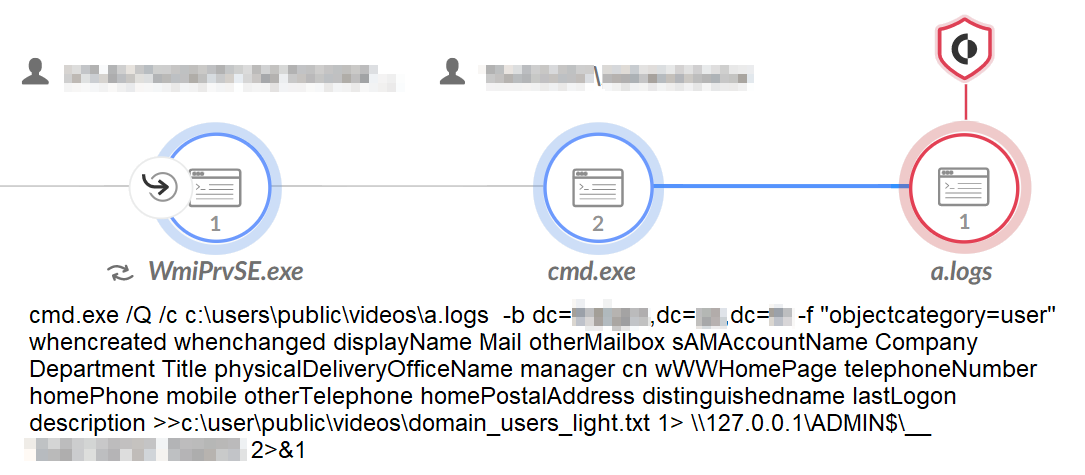
Als Teil einer Kampagne, die von 2021 bis 2023 auf Regierungsstellen in Südostasien abzielte, wurde Stately Taurus mit der Verwendung von AdFind während der Aufklärungsphase des Angriffs in Verbindung gebracht.
AdFind ist ein Befehlszeilen-Abfragetool, das für die LDAP-Aufzählung verwendet werden kann, indem es Informationen von einem Active Directory-Domänencontroller sammelt. Während des Angriffs benannten die Bedrohungsakteure das Tool von adfind.exe in a.logs um, um die Erkennung zu umgehen.
Abbildung 3 zeigt einen Screenshot aus einer Cortex XDR-Warnung, in der der Bedrohungsakteur versucht, die Ergebnisse einer AdFind-Abfrage unter den folgenden Dateinamen zu speichern:
- Domain_benutzer_licht.txt
- Bereich_Rechner_licht.txt
- Bereich_Gruppen_licht.txt
Der ehrgeizige Scorpius setzte ADRecon bei Ransomware-Operationen ein
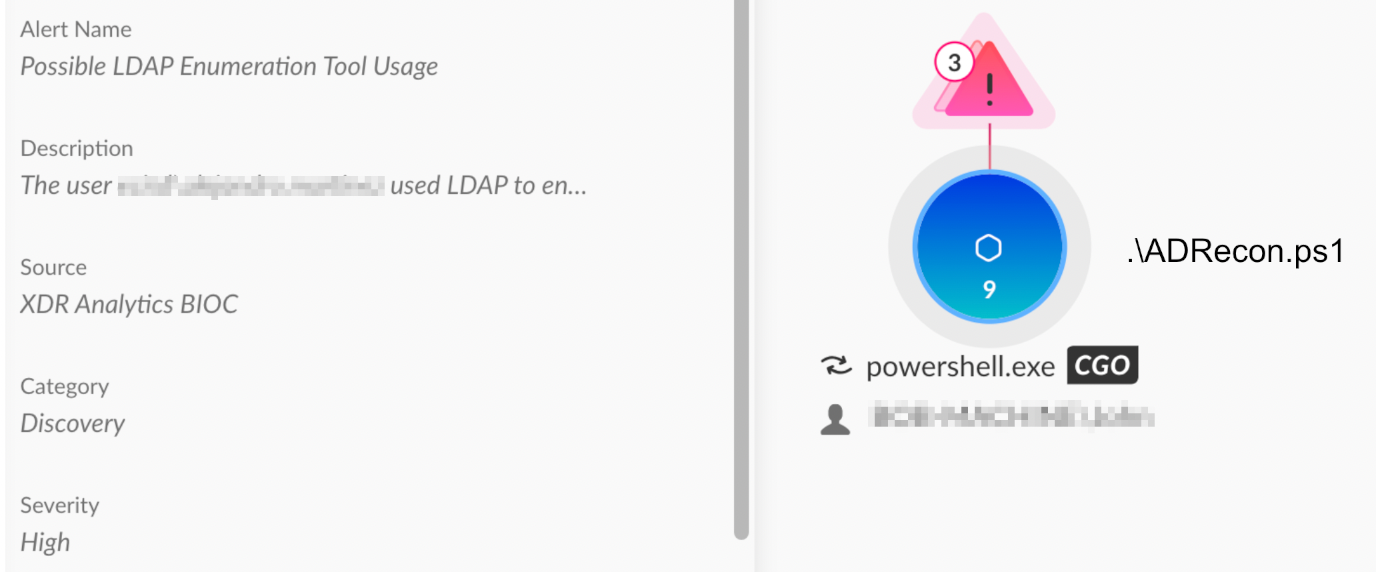
Mitglieder der BlackCat (ALPHV) Ransomware-Gruppe, die wir als Ambitious Scorpius verfolgen, haben ADRecon bei mehreren Angriffen verwendet. ADRecon ist ein PowerShell-Skript, das mithilfe von LDAP Informationen über eine Active Directory-Umgebung sammelt und einen Bericht erstellt, der eine Momentaufnahme des Zielnetzwerks liefert.
Aufgrund der fortgesetzten Nutzung von ADRecon durch diese Gruppe gehen wir davon aus, dass das Tool Teil des Ambitious Scorpius Playbooks sein könnte. Abbildung 4 zeigt eine Cortex-XDR-Warnung zur Erkennung und Verhinderung von ADRecon-Aktivitäten.
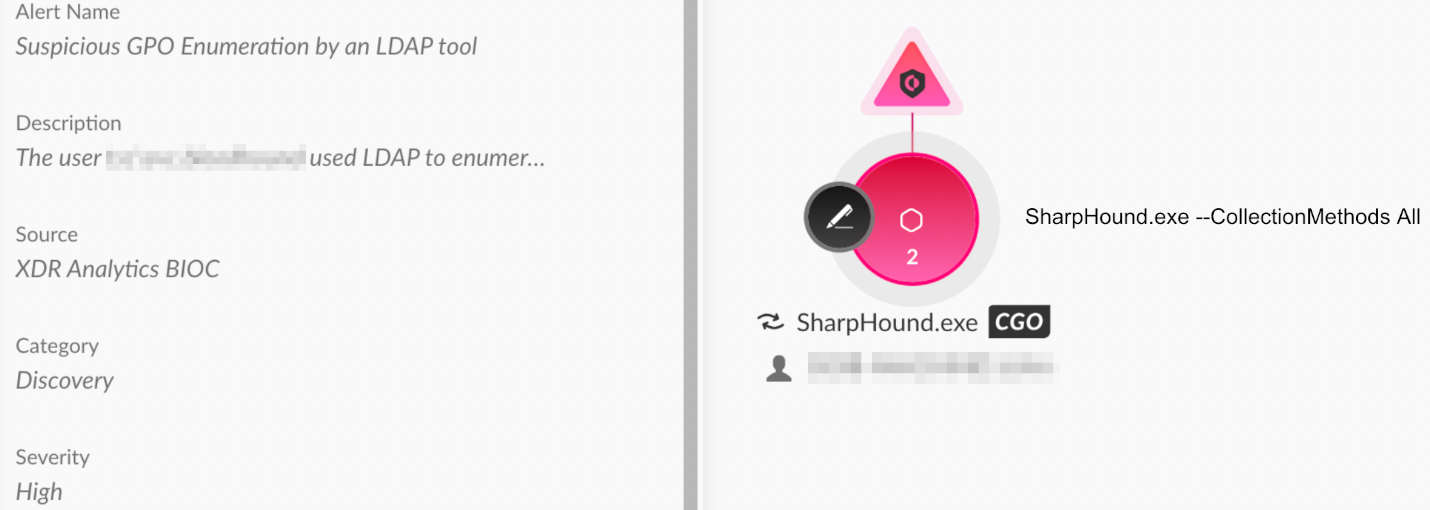
SharpHound in einer IcedID und Dagon Locker Ransomware Operation verwendet
Im April 2024 beschrieb der DFIR-Bericht einen Einbruch mit IcedID-Malware und Dagon Locker-Ransomware. Während dieses Eindringens verwendeten die Angreifer SharpHound, um Daten über die Active Directory-Umgebung zu sammeln.
SharpHound ist eine Datensammelkomponente von BloodHound. Sie nutzt die Windows-API und LDAP-Funktionen, um Daten von Domänencontrollern und Windows-Systemen, die Teil der Domäne sind, zu sammeln. Abbildung 5 zeigt die Erkennung und Verhinderung von SharpHound in Cortex XDR.
Erkennungsstrategien für LDAP-basierte Angriffe
Zur effektiven Erkennung von LDAP-basierten Angriffen gehört die Überwachung von LDAP-Protokollen auf verdächtige Aktivitäten. Ereignisprotokolle erfassen wichtige Daten, darunter:
- Besuchte Einträge: Dies ist die Gesamtzahl der durchgeführten LDAP-Abfragen.
- Zurückgegebene Einträge: Hier werden die tatsächlichen Ergebnisse dieser Abfragen oder deren Anzahl angegeben.
Legitime LDAP-Abfragen zielen in der Regel auf bestimmte Objekte oder Attribute ab, was zu weniger besuchten und zurückgegebenen Einträgen führt. Bei Aufzählungsversuchen hingegen werden breitere Abfragen verwendet, da die Angreifer versuchen, so viele Informationen wie möglich zu sammeln, indem sie alle Benutzer, Computer oder Gruppen abfragen.
Nachfolgend finden Sie die wichtigsten Erkennungsstrategien, mit denen Sie LDAP-Aufzählungsversuche erkennen und abwehren können:
1. Besuchte und zurückgegebene Einträge
Überprüfen Sie die Protokolle auf Ereignisse mit der Ereignis-ID 1644, sowohl für besuchte als auch für zurückgegebene Einträge.
- Niedriges Verhältnis zwischen Besuchen und Rücksendungen: Diese niedrige Quote ist typisch für legitime Abfragen, die auf eine breite Palette von Objekten abzielen.
- Hohe Summe der zurückgegebenen Einträge: Dies deutet auf einen Versuch hin, große Mengen an Verzeichnisdaten zu sammeln. Dies ist ein möglicher Hinweis auf eine Aufzählung durch einen Angreifer.
2. Benutzerkontext
Die Analyse von LDAP-Abfragen nach dem Benutzerkontext kann auch Aufzählungsaktivitäten aufdecken:
- Titel oder Rolle des Benutzers: Überlegen Sie, ob die LDAP-Aktivität zur typischen Rolle des Benutzers passt. Beispielsweise könnten Servicekonten und IT-Mitarbeiter rechtmäßig umfangreiche LDAP-Abfragen durchführen. Wenn jedoch ein Benutzer außerhalb dieser Rollen eine ähnliche Aktivität durchführt, könnte dies ein Hinweis auf eine mögliche Aufzählung sein.
- Suche nach Umfangsanomalien: Nutzer, die ihren Suchbereich plötzlich über typische Muster hinaus erweitern, könnten eine Erkundung durchführen.
3. Basislinie und Anomalien
Die Erstellung einer Basislinie für LDAP-Abfragedaten kann dazu beitragen, Anomalien oder Abweichungen vom Standardverhalten von Benutzern und Maschinen aufzudecken. Diese Strategie besteht aus drei Komponenten:
- Normalisierung: Standardisierung von Abfragedaten zur Ermittlung von Mustern und Abweichungen
- Vertrieb: Verfolgen, wie viele Rechner eine Abfrage ausgeführt haben
- Vielfalt der Nutzer: Überwachen, wie viele Benutzer eine Abfrage ausgeführt haben
4. LDAP-Abfragefilter
Da Angreifer verschiedene LDAP-Abfragefilter verwenden, um Verzeichnisdaten zu extrahieren, weist eine Vielzahl dieser Filter in LDAP-Abfrageprotokollen häufig auf Enumeration-Aktivitäten hin. Die Art des LDAP-Abfragefilters kann Aufschluss über die Art der Aufzählung geben. Einige gängige Arten der LDAP-Aufzählung, die überwacht werden sollten, sind:
- Admin-Aufzählung: Abfragen, die auf administrative Konten und Berechtigungen abzielen
- Aufzählung der Dienstkonten: Identifizierung von Dienstkonten und deren Konfigurationen
- GPO-Aufzählung: Abruf von Gruppenrichtlinienobjekten und deren Einstellungen
- Aufzählung der Domänenrechner: Sammeln von Informationen über Maschinen unter derselben Domäne
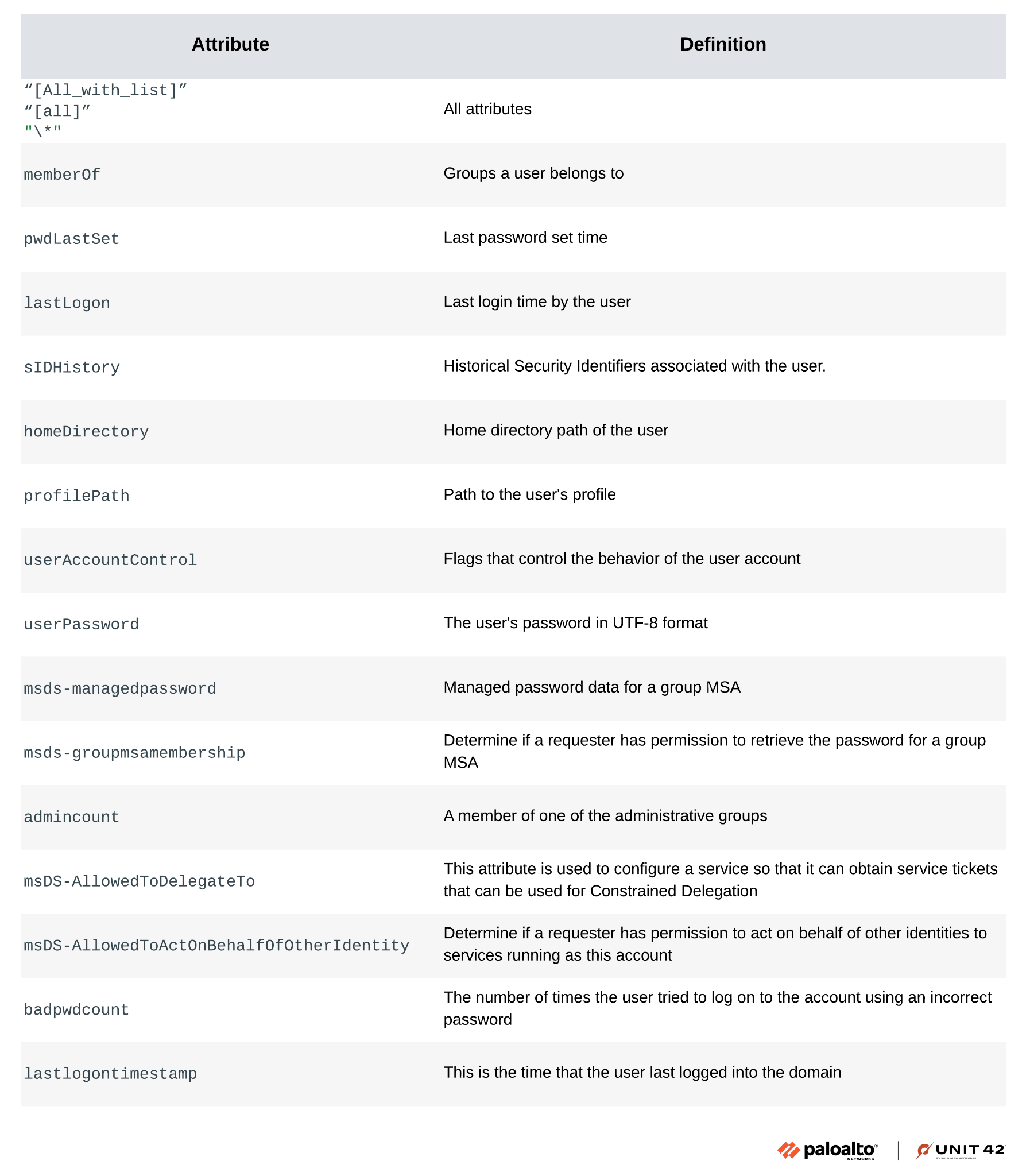
5. Verdächtige Attribute
Die Überwachung von Abfragen für bestimmte Attribute wie memberOf, pwdLastSet, lastLogon und admincount kann helfen, verdächtige Aktivitäten zu erkennen.
Angreifer verwenden in der Regel die folgenden Attribute in LDAP-Abfragen:
- admincount
- badpwdcount
- homeDirectory
- lastLogon
- memberOf
- msDS-AllowedToActOnBehalfOfOtherIdentity
- msDS-AllowedToDelegateTo
- msds-groupmsamembership
- msds-managedpassword
- profilPfad
- pwdLastSet
- sIDHistory
- userAccountControl
- userPasswort
Anhang A zeigt ein Beispiel für eine XQL-Abfrage in Cortex XDR, um die oben genannten LDAP-Attribute zu verfolgen.
Abbildung 6 zeigt eine Tabelle mit Beispielen von LDAP-Attributen, einschließlich ihrer Definitionen und möglichen Auswirkungen auf die Sicherheit.
Schlussfolgerung
LDAP ist ein zweischneidiges Schwert in Active Directory. Es ist für die Verwaltung unerlässlich, aber auch anfällig für Angriffe. Während LDAP die Verzeichnisverwaltung vereinfacht, können Angreifer seine leistungsstarken Abfragefunktionen ausnutzen, um sensible Informationen zu sammeln.
Dieser Artikel beleuchtet die Herausforderungen bei der Erkennung bösartiger LDAP-Aktivitäten. Er enthält außerdem Beispiele aus der Praxis für LDAP-Aufzählungsangriffe sowie praktische Tipps zur Erkennung.
Das Verständnis und die Überwachung der LDAP-Aufzählung in Verbindung mit robusten Erkennungsstrategien sind für die Risikominderung und die Sicherung von Verzeichnisdiensten unerlässlich.
Schutzmaßnahmen und Abhilfemaßnahmen
Für Kunden von Palo Alto Networks bieten unsere Produkte und Dienste die folgende Abdeckung:
- Cortex XDR und XSIAM sind dafür ausgelegt:
- Schutz vor der Ausnutzung verschiedener Schwachstellen sowie vor bösartigen Verhaltensweisen durch Behavioral Threat Protection.
- Erkennen Sie benutzer- und anmeldungsbasierte Bedrohungen durch die Analyse von Benutzeraktivitäten aus verschiedenen Datenquellen, einschließlich Endgeräten, Netzwerk-Firewalls, Active Directory, Identitäts- und Zugriffsmanagementlösungen und Cloud-Workloads. Cortex erstellt mithilfe von maschinellem Lernen Verhaltensprofile von Benutzeraktivitäten im Laufe der Zeit. Es erkennt anomale Aktivitäten, die auf auf Anmeldeinformationen basierende Angriffe hindeuten, indem es neue Aktivitäten mit früheren Aktivitäten, Peer-Aktivitäten und dem erwarteten Verhalten der Entität vergleicht.
- Erkennen Sie LDAP-Netzwerkangriffe, einschließlich der in diesem Artikel erwähnten, mit Verhaltensanalysen durch Cortex XDR Pro und XSIAM.
- Schutz vor nachträglicher Ausbeutung durch einen mehrschichtigen Ansatz.
- Cortex XSIAM hat ein Suspicious LDAP Search Query Playbook veröffentlicht, um die Reaktion auf analytische LDAP-Warnungen zu verbessern. Dieses Playbook bewertet den Risikowert der beteiligten Entitäten, untersucht die Häufigkeit der damit verbundenen Prozesse und überprüft die ausgeführte Befehlszeile auf verdächtige Parameter. Wird während der Untersuchungsphase eine verdächtige Aktivität festgestellt, beendet das Playbook den Kausalitätsprozess als Abhilfemaßnahme.
- Cortex Xpanse und das ASM-Modul für XSIAM sind in der Lage, über das Internet zugängliche LDAP-Server zu erkennen.
Wenn Sie glauben, dass Sie betroffen sein könnten, oder ein dringendes Anliegen haben, wenden Sie sich an das Team von Unit 42 Incident Response oder rufen Sie an:
- Gebührenfrei für Nordamerika: 866.486.4842 (866.4.UNIT42)
- EMEA: +31.20.299.3130
- APAC: +65.6983.8730
- Japan: +81.50.1790.0200
Palo Alto Networks hat diese Erkenntnisse, einschließlich Dateimustern und Kompromissindikatoren, mit den anderen Mitgliedern der Cyber Threat Alliance (CTA) geteilt. CTA-Mitglieder nutzen diese Erkenntnisse, um ihren Kunden schnell Schutzmaßnahmen zu bieten und böswillige Cyber-Akteure systematisch zu stören. Erfahren Sie mehr über die Cyber Threat Alliance.
Zusätzliche Ressourcen
- Cyberspionage-Angriffe gegen die südostasiatische Regierung stehen in Verbindung mit dem stattlichen Taurus, auch bekannt als Mustang Panda - Unit 42, Palo Alto Networks
- Die Anatomie eines BlackCat (ALPHV)-Angriffs - Sygnia
- Die vielen Leben der BlackCat-Ransomware - Microsoft
- Von IcedID zu Dagon Locker Ransomware in 29 Tagen - Der DFIR-Bericht
- SharpHound - BloodHound 4.3.1 Dokumentation - BloodHound
Anhang A
Die folgende XQL-Abfrage in Cortex verfolgt LDAP-Abfrageattribute, auf die Angreifer häufig abzielen:
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
|
Datensatz = xdr_data // Verwendung des xdr-Datensatzes
| Filter ereignis_art = ENUM.EVENT_LOG und action_evtlog_event_id in (1644, 30)
| ändern
evtlog_ldap_domain_service_attributes = json_extract_scalar(action_evtlog_data_fields, "$.param7"),
ldap_attribute_liste = json_extract_scalar(action_evtlog_data_fields, "$.AttributListe"),
ldap_1644_search_filter = json_extract_scalar(action_evtlog_data_fields, "$.param2"),
ldap_30_such_filter = json_extract_scalar(action_evtlog_data_fields, "$.SearchFilter")
| ändern
Attribut_liste = Kleinbuchstaben(verschmelzen(evtlog_ldap_domain_service_attributes, ldap_attribute_liste)),
such_filter = Kleinbuchstaben(verschmelzen(ldap_30_such_filter, ldap_1644_search_filter))
| ändern attribut_regex_check = regextract(
Attribut_liste,
"All_with_list|all|memberOf|pwdLastSet|lastLogon|sIDHistory|homeDirectory|profilePath|userAccountControl|userPassword|msds-managedpassword|msds-groupmsamembership|admincount|msDS-AllowedToDelegateTo|badpwdcount|msDS-AllowedToActOnBehalfOfOtherIdentity"
)
| Filter attribut_regex_check != Null
// Spamming-Anfragen herausfiltern
| Filter such_filter != "(objectclass=*)"
| Filter such_filter != "(objectcategory=*)"
| Felder Attribut_liste, attribut_regex_check, action_evtlog_data_fields, actor_process_image_name, such_filter
|
Anhang B
Einblick in LDAP-Abfragen und -Tools
Grundlagen von LDAP-Abfragefiltern
LDAP-Abfragen rufen Verzeichnisobjekte wie Benutzer, Gruppen oder Computer auf der Grundlage bestimmter Filter ab. Dieser Abschnitt enthält Beispiele für Abfragefilter, die Systemadministratoren für legitime Zwecke verwenden können, die aber auch von Angreifern für böswillige Zwecke genutzt werden könnten.
Um zum Beispiel alle Benutzerkonten in einer Active Directory-Umgebung zu finden, können wir den folgenden Abfragefilter verwenden:
|
1
|
(&(objectClass=Benutzer)(ObjektKategorie=Person))
|
Darüber hinaus können wir Abfragen verfeinern, um spezifische Anforderungen zu erfüllen, indem wir dem Abfragefilter weitere Attribute hinzufügen. Um z. B. Benutzer in privilegierten Gruppen zu finden, können wir diesen LDAP-Abfragefilter verwenden:
|
1
|
(&(objectClass=Benutzer)(ObjektKategorie=Person)(adminCount=1))
|
In den obigen Beispielen wird das Symbol & verwendet, das ein logischer UND-Operator ist und bedeutet, dass alle angegebenen Bedingungen erfüllt sein müssen. LDAP unterstützt logische Operatoren für erweiterte Filterung:
- UND (&): Stellt sicher, dass alle angegebenen Bedingungen erfüllt sein müssen
- OR (|): Erlaubt die Erfüllung einer der folgenden Bedingungen
- NICHT (!): Schließt Objekte aus, die eine bestimmte Bedingung erfüllen
Tools für die LDAP-Aufzählung
Angreifern steht eine Reihe von Tools für die LDAP-Aufzählung zur Verfügung. In Abbildung 7 sind einige dieser wichtigen Tools dargestellt. Abbildung 7 zeigt auch Beispiele für Abfragen, die jedes Tool ausführen kann:
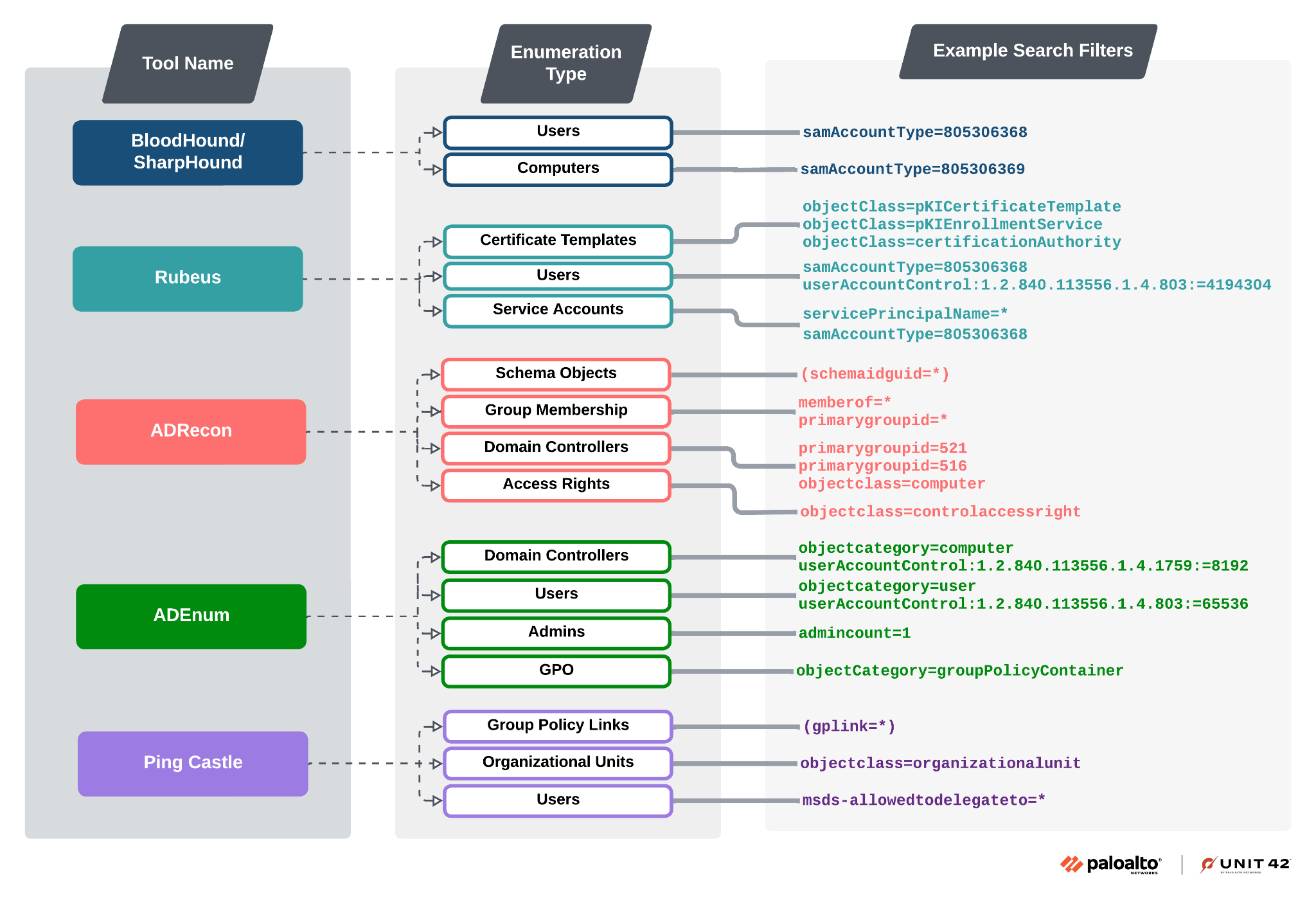
Jedes Tool erleichtert verschiedene Arten von LDAP-Abfragen, mit denen Angreifer Active Directory-Umgebungen abbilden und so wichtige Ziele wie Dienstkonten und privilegierte Benutzer identifizieren können.
Analyse von LDAP-Aufzählungsabfrageattributen
Um bösartige Aktivitäten in Active Directory-Umgebungen zu erkennen, ist es wichtig, die Art der von Angreifern verwendeten LDAP-Aufzählungsabfragen zu verstehen. Im Folgenden werden einige gängige Abfragen und ihre potenziellen Risiken erläutert:
Benutzer mit deaktivierter Kerberos-Vorauthentifizierung
|
1
|
userAccountControl:1.2.840.113556.1.4.803:=4194304
|
- Beschreibung: Das Attribut userAccountControl wird verwendet, um Benutzerkonten zu identifizieren, bei denen die Kerberos-Vorauthentifizierung deaktiviert ist. Diese Einstellung ist eine Schlüsselbedingung für den AS-REP-Röstangriff.
- Risiko: Angreifer können von diesen Konten AS-REP-Tickets anfordern und möglicherweise knacken, was zu unberechtigtem Zugriff führen kann.
Service-Konten
|
1
|
servicePrincipalName=*
|
- Beschreibung: Identifiziert Benutzerkonten, die über SPN-Einträge (Service Principal Name) verfügen.
- Risiko: SPNs werden bei der Kerberos-Authentifizierung verwendet, um Dienstinstanzen mit Benutzerkonten zu verknüpfen. Angreifer nutzen diese Informationen, um Kerberoasting-Angriffe durchzuführen, bei denen sie versuchen, Diensttickets zu knacken.
Active Directory-Benutzer aufzählen
|
1
|
samAccountType=805306368
|
- Beschreibung: Das Attribut samAccountType mit dem Wert 805306368 spezifiziert Active Directory-Benutzerkonten.
- Risiko: Eine LDAP-Abfrage mit diesem Attribut liefert eine Liste aller Benutzerkonten, die für weitere Aufzählungen oder zur Identifizierung von Angriffszielen verwendet werden kann.



