At SandboxAQ, we recently delved into Signal Desktop to identify how its key management could be improved by using security hardware. Our analysis highlights the need for robust and consistent key isolation services across desktop platforms. In this blogpost,
- We analyse the security of Signal Desktop’s key management in light of recent attack reports, and
- We show how security hardware can protect Signal Desktop’s keys with a proof of concept (PoC)—a fork of Signal Desktop—and explore the tradeoffs with this approach.
Signal is an open-source messaging service that implements end-to-end encryption. Its users benefit from best-in-class privacy when communicating online.1 This level of privacy is made possible by the Signal protocol, considered the gold standard of end-to-end encrypted messaging. Its security protocol depends on cryptographic keys handled on-device. For mobile devices, Signal securely stores them in isolated and controlled locations. However, when it comes to desktop, Signal (just like everyone else) must do without OS-provided secure key management capabilities.
The problem
It all starts with a Twitter post explaining how an attacker running malware could extract all Signal Desktop’s confidential data and run a clone of the victim’s messaging application. This attack was possible because, although Signal encrypts the local database containing confidential data (including messages and keys), it stored the database decryption keys in plaintext.
Attack scenario
- Attacker gains access to the local Signal database encryption key. This can be accomplished through either (a) physical access to the disk at rest, bypassing disk encryption, or (b) malware operating with the victim’s privilege rights, like a malicious app.
- Attacker decrypts the database and extracts its data. Given that the database encryption was saved in plaintext, this process is straightforward.2
- Attacker impersonates the victim or compromises their messages. The compromised database contains the victim’s conversation history on this device and a set of keys used in the Signal protocol.
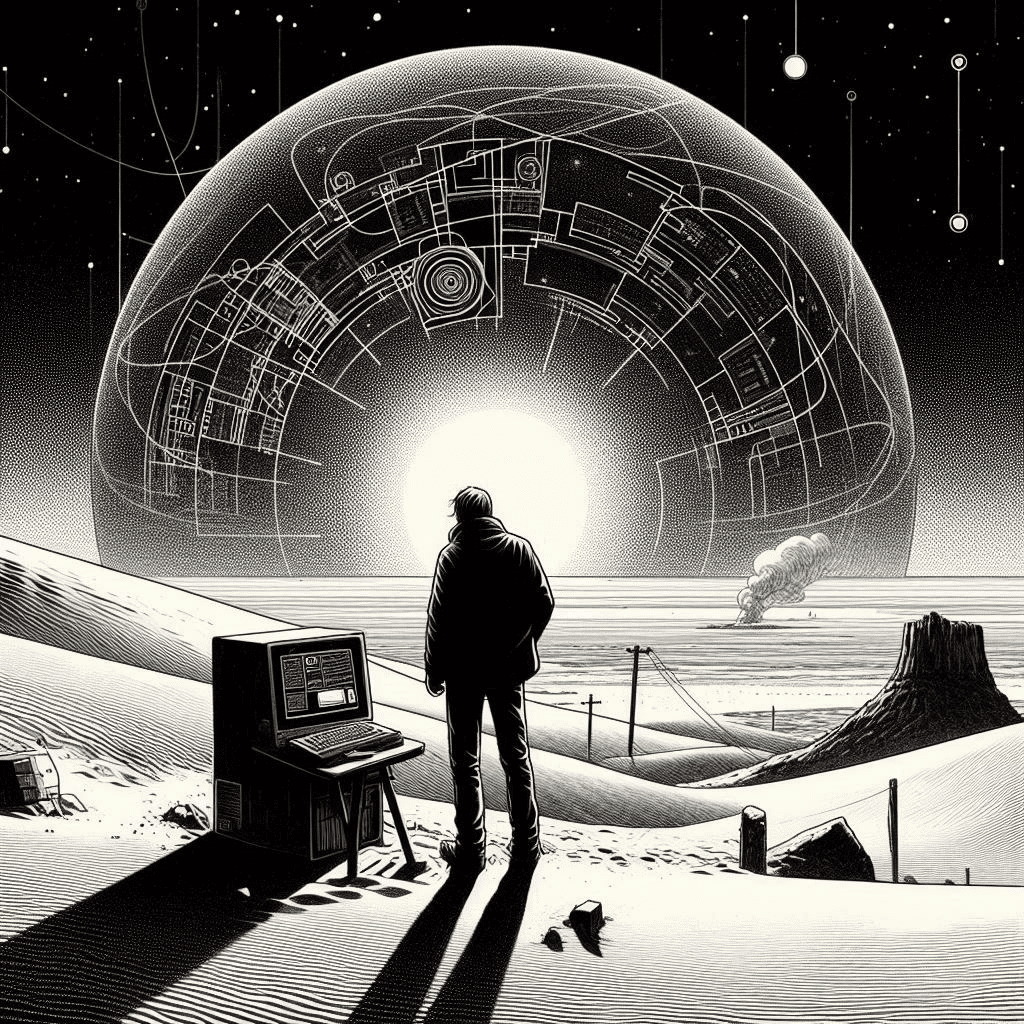
Here’s a visual representation of the attack vector.